Importance of External Network Pen Testing Services
While internal security is crucial, external vulnerabilities can expose your organization to significant risks. External network penetration testing evaluates your network's resilience against real-world cyber attacks originating from outside your organization. By simulating sophisticated attacker techniques, we uncover security weaknesses that could lead to unauthorized access, data breaches, or service disruptions.
Protect Internet-Facing Assets
Identify vulnerabilities in web servers, VPN gateways, firewalls, and other public-facing infrastructure.
Prevent Unauthorized Access
Detect weak authentication mechanisms or misconfigurations that could allow attackers to infiltrate your network.

Safeguard Sensitive Data
Ensure that data transmitted over external networks is secure from interception or manipulation.
Maintain Business Continuity
Prevent cyberattacks that could lead to downtime, financial loss, or reputational damage.
Compliance Requirements
Meet regulatory standards that mandate regular security assessments, such as PCI DSS, HIPAA, and GDPR.
What Can External Network Penetration Testing Services Detect?
Our external network penetration testing services can uncover a wide range of vulnerabilities and security issues, including:
Open Ports and Services
Identification of unnecessary or unsecured services that could be exploited.
Misconfigurations
Detection of improperly configured firewalls, routers, or security devices.
Outdated Software
Discovery of unpatched systems vulnerable to known exploits.
Weak Authentication Mechanisms
Identification of weak passwords, default credentials, or inadequate multi-factor authentication.
SSL/TLS Vulnerabilities
Analysis of encryption protocols to ensure secure data transmission.
Application Layer Vulnerabilities
Detection of issues like SQL injection, cross-site scripting (XSS), and other web application flaws.
DNS and Email Security Flaws
Identification of vulnerabilities in DNS configurations and email servers that could lead to phishing or spoofing attacks.
Exposure of Sensitive Information
Detection of data leakage through error messages, directory listings, or misconfigured services.
Our External Network Penetration Testing Methodology
Our comprehensive external network penetration testing methodology is rooted in industry best practices and frameworks such as NIST, OWASP, and PTES. We employ both automated tools and meticulous manual testing to ensure thorough coverage:
Reconnaissance and Information Gathering
Vulnerability Identification
Exploitation Attempts
Post-Exploitation Analysis
Reporting and Recommendations
Post-Engagement Support
Reconnaissance and Information Gathering
-
Asset Enumeration
Identify all public-facing IP addresses, domains, and services.
-
Passive Reconnaissance
Gather information from public sources to understand potential attack vectors.
-
Active Scanning
Use advanced tools to detect open ports, services, and system banners.
Vulnerability Identification
-
Automated Scanning
Utilize industry-leading tools to detect known vulnerabilities.
-
Manual Verification
Validate automated findings and uncover additional vulnerabilities through expert analysis.
-
Configuration Reviews
Examine external device configurations for weaknesses.
Exploitation Attempts
-
Targeted Attacks
Simulate real-world attack scenarios to exploit identified vulnerabilities.
-
Privilege Escalation
Attempt to gain higher-level access to systems and data.
-
Network Mapping
Discover potential paths to internal networks through exposed services.
Post-Exploitation Analysis
-
Data Exfiltration Testing
Assess the ability to extract sensitive data from compromised systems.
-
Persistence Mechanisms
Evaluate how an attacker could maintain access over time.
-
Cleanup Procedures
Ensure no residual impact on systems after testing.
Reporting and Recommendations
-
Detailed Findings
Provide comprehensive reports with technical details, impact assessments, and remediation steps.
-
Risk Prioritization
Rank vulnerabilities based on severity and exploitability.
-
Strategic Guidance
Offer recommendations for immediate fixes and long-term security enhancements.
Post-Engagement Support
-
Remediation Assistance
Work with your team to address and resolve identified issues.
-
Validation Testing
Re-test to confirm that vulnerabilities have been effectively remediated.
-
Ongoing Partnership
Develop a roadmap for continuous security improvement.
Why Choose Our External Network Penetration Testing Services
Iterasec external network pentesting services are distinguished by our:Expert Cybersecurity Team
Our team of security experts finds juicier and more complex security vulnerabilities than other vendors.
Pragmatic Approach
We start with threat modeling and tailor our testing methodologies to suit your specific application requirements.
Delivery Quality
On-time, clear communication, proactive. Underpromise, overdeliver – that’s our motto.
Contact us today to discuss how our external network penetration testing can help secure your organization against external threats.
Contact usOur Expert Cybersecurity Team
Cybersecurity is an industry of constant learning. Each of our colleagues has a professional and certification development plan.
Discover All Steps of Iterasec External Network Pentesting Process
During our pentests we rely on the NIST, OWASP, OSSTM, CIS Benchmark and other methodologies. While employing some automated tools, we mostly perform manual expert penetration testing: such an approach proves to be the most practically valuable.
We keep clients informed in the course of the project, providing regular status updates and immediate notifications for critical findings.
- 1A kick-off meeting to agree on the scope, inputs and communication
- 2Cloud pentest (2-5 weeks, depending on the scope)
- 3The final report that highlights the identified cloud security issues
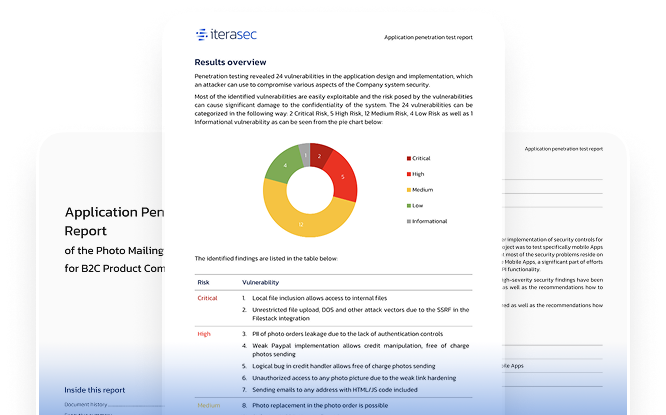
Explore our sample penetration testing service report
Please contact us, and we will send you a sample pentest report covering several applications.
Contact usWhat our clients say
Awards and Recognitions
2023
Top cybersecurity consulting company
2023
Top cybersecurity consulting company
2023
Top ponetration testing company
Related Cyber Security Services
FAQs
It’s recommended to conduct external network penetration testing at least annually or whenever significant changes are made to your external infrastructure. Regular testing ensures that new vulnerabilities are identified and addressed promptly.
The duration of an external network penetration test depends on the size and complexity of your network. Typically, tests can range from a few days to a couple of weeks. We work with you to establish timelines that suit your operational needs.
External network penetration testing can detect a variety of threats, including open ports, misconfigurations, outdated software, weak authentication mechanisms, and vulnerabilities in web applications or services that are exposed to the internet.
External network penetration testing focuses on identifying vulnerabilities that could be exploited by attackers from outside your organization’s network perimeter. Internal testing, on the other hand, simulates attacks from within the network, assessing risks related to insider threats or breaches that have bypassed external defenses.
By proactively identifying and remediating vulnerabilities in your external network, penetration testing reduces the attack surface available to cybercriminals. It helps prevent unauthorized access, data breaches, and other cyberattacks by ensuring your perimeter defenses are robust and up-to-date.
Contacts
Please tell us what are you looking for and we will happily support you in that. Feel free to use our contact form or contact us directly.
Thank you for submission!
We’ve received your request and will get back to you shortly. If you have any urgent questions, feel free to contact us at [email protected]