Importance of Internal Network Pen Testing Services
While external threats often grab headlines, internal vulnerabilities can be just as damaging. Insider threats, whether malicious or accidental, along with compromised devices and inadequate security policies, can expose your network to significant risks. By conducting an internal network penetration test, you proactively address these risks, safeguarding your assets and maintaining the trust of clients and stakeholders:

Insider Threats
Employees or contractors with access to sensitive systems may intentionally or unintentionally cause security breaches.
Compromised Devices
Laptops, smartphones, or IoT devices connected to the internal network can introduce malware or provide entry points for attackers.
Policy Gaps
Weak or unenforced security policies can leave your network vulnerable to unauthorized access or data leakage.
Hidden Risks
Identify weaknesses in internal systems, configurations, and access controls that are not visible from the outside.
Our Internal Network Penetration Testing Methodology
Our methodology is built upon industry-recognized frameworks, we combine advanced technical expertise with a deep understanding of internal network security challenges to deliver thorough and effective assessments. Following this meticulous methodology, our internal network penetration testing services identify existing vulnerabilities and strengthen your network's defenses against future threats:
In-Depth Threat Modeling
Comprehensive Vulnerability Assessment
Advanced Exploitation Techniques
Specialized Testing Modules
Continuous Engagement and Adaptation
Rigorous Analysis and Reporting
Post-Engagement Support
In-Depth Threat Modeling
-
Asset Identification
Catalog critical assets, including servers, workstations, network devices, and data repositories.
-
Trust Relationships Mapping
Analyze relationships between systems and users to identify potential abuse of privileges.
-
Attack Vector Analysis
Identify potential internal threats, such as malicious insiders, compromised devices, or inadequate access controls.
Comprehensive Vulnerability Assessment
-
Configuration Reviews
Examine system and device configurations for weaknesses like default settings or unnecessary services.
-
Patch Level Verification
Check for missing security updates on operating systems and applications.
-
Access Control Testing
Assess the effectiveness of permissions and user roles in preventing unauthorized access.
-
Network Segmentation Analysis
Evaluate the design and implementation of network segmentation to prevent unauthorized movement between network zones.
Advanced Exploitation Techniques
-
Privilege Escalation Attempts
Use techniques to gain higher-level access from standard user accounts, mimicking potential insider threats.
-
Lateral Movement Simulation
Test the ability to move through the network horizontally, accessing additional systems or data.
-
Password Cracking and Credential Harvesting
Attempt to retrieve and crack password hashes to evaluate password policies and storage practices.
-
Bypassing Security Controls
Challenge the effectiveness of internal firewalls, intrusion detection systems (IDS), and endpoint protections.
Specialized Testing Modules
-
Active Directory (AD) Security Assessment
Evaluate AD configurations for vulnerabilities like weak group policies, exposed LDAP services, or Kerberos ticket attacks.
-
Wireless Network Security
Test the security of internal wireless networks against unauthorized access and eavesdropping.
-
Endpoint Security Evaluation
Assess antivirus effectiveness, application whitelisting, and device hardening measures.
-
Data Leakage Prevention
Check for potential data exfiltration paths and the effectiveness of monitoring and prevention controls.
Continuous Engagement and Adaptation
-
Collaborative Testing
Work closely with your security team to understand existing controls and avoid disrupting operations.
-
Dynamic Strategy Adjustment
Modify testing techniques in response to initial findings to thoroughly explore potential vulnerabilities.
-
Knowledge Transfer
Share insights and educate your team on detected issues and prevention strategies.
Rigorous Analysis and Reporting
-
Detailed Technical Findings
Include comprehensive descriptions, impact assessments, and replication steps for each vulnerability.
-
Risk Prioritization
Rank vulnerabilities based on their potential impact and likelihood of exploitation within your environment.
-
Strategic Recommendations
Offer both immediate remediation actions and long-term security improvement strategies.
-
Executive Summaries
Provide high-level overviews suitable for non-technical stakeholders to understand risks and required investments.
Post-Engagement Support
-
Remediation Guidance
Assist your team in interpreting findings and implementing effective fixes.
-
Validation Testing
Re-assess remediated vulnerabilities to confirm their resolution.
-
Security Roadmap Development
Help develop a plan for ongoing security enhancements and future testing cycles.
Why Choose Our Internal Network Penetration Testing Services
Iterasec internal network pentesting services are distinguished by our:Expert Cybersecurity Team
Our team of security experts finds juicier and more complex security vulnerabilities than other vendors.
Pragmatic Approach
We start with threat modeling and tailor our testing methodologies to suit your specific application requirements.
Delivery Quality
On-time, clear communication, proactive. Underpromise, overdeliver – that’s our motto.
Ready to protect your critical assets? Get in touch to discuss how we can help safeguard your internal network.
Contact usOur Expert Cybersecurity Team
Cybersecurity is an industry of constant learning. Each of our colleagues has a professional and certification development plan.
Discover All Steps of Iterasec Internal Network Pentesting Process
During our pentests we rely on the NIST, OWASP, OSSTM, CIS Benchmark and other methodologies. While employing some automated tools, we mostly perform manual expert penetration testing: such an approach proves to be the most practically valuable.
We keep clients informed in the course of the project, providing regular status updates and immediate notifications for critical findings.
- 1A kick-off meeting to agree on the scope, inputs and communication
- 2Cloud pentest (2-5 weeks, depending on the scope)
- 3The final report that highlights the identified cloud security issues
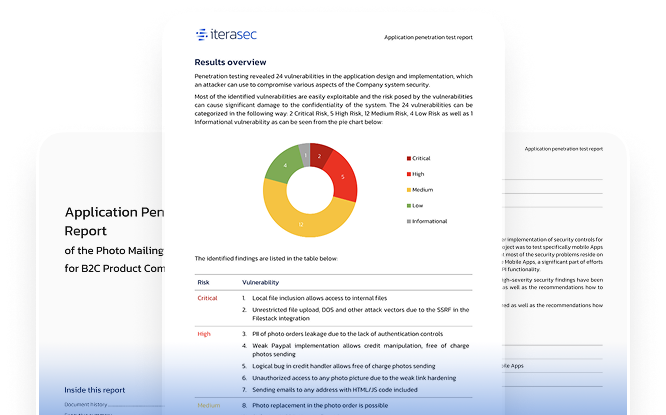
Explore our sample penetration testing service report
Please contact us, and we will send you a sample pentest report covering several applications.
Contact usWhat our clients say
Awards and Recognitions
2023
Top cybersecurity consulting company
2023
Top cybersecurity consulting company
2023
Top ponetration testing company
Related Cyber Security Services
FAQs
The process starts with defining the scope and gathering information about your network. Vulnerabilities are identified using automated tools and manual techniques, followed by simulated attacks to assess their impact. Afterward, we provide a detailed report with remediation steps and support to fix the identified issues.
Penetration testing strengthens your security by uncovering and addressing internal vulnerabilities before they are exploited. It improves access controls, enhances network segmentation, and ensures compliance with regulations, all while reducing the risk of internal and external threats.
This type of testing can identify a range of vulnerabilities that exist within your internal network, such as weak access controls, outdated or unpatched software, and misconfigured network devices. Testing may also reveal issues with insufficient authentication mechanisms, insecure network segmentation, or the exposure of sensitive data. By identifying these vulnerabilities, you gain insight into areas that require immediate attention to avoid internal threats or breaches.
It’s recommended to conduct tests annually or after significant changes to the network infrastructure, such as system upgrades, policy changes, or after introducing new technologies.
Our testing methodologies are designed to minimize any impact on your operations. We work closely with your team to schedule tests during appropriate times and ensure all precautions are in place.
Contacts
Please tell us what are you looking for and we will happily support you in that. Feel free to use our contact form or contact us directly.
Thank you for submission!
We’ve received your request and will get back to you shortly. If you have any urgent questions, feel free to contact us at [email protected]