Why Mobile Application Penetration Testing Services are Important
Mobile applications face unique security challenges, from insecure data storage to vulnerabilities in APIs and network communications. Penetration testing for mobile applications is essential to uncovering hidden flaws that could expose your users and your business to risks. Mobile app pentesting services help ensure your app is resilient against the latest attack methods and security threats.
What to Expect from our Mobile App Pentesting Services
At Iterasec, our mobile app pentesting services cover a wide range of mobile platforms and frameworks, ensuring your app is secure regardless of the technology used. We tailor each mobile app pentest to the specific environment and technology your app is built on, ensuring comprehensive protection against platform-specific risks. We conduct thorough penetration testing on:
What Our Mobile App Pen Test Can Detect? Common Vulnerabilities in Mobile Apps
We tailor each penetration test to your app’s environment, ensuring comprehensive protection from mobile-specific threats. Our mobile app pen test identifies and assesses a variety of vulnerabilities, including:
Data Leakage
Sensitive data like user credentials or personal information can be exposed through insecure storage or unencrypted communication, leading to breaches and compromised user privacy.
Improper Session Handling
Weak session management, such as insecure tokens or lack of proper expiration, can allow attackers to hijack sessions, gaining unauthorized access to user accounts or data.
Code Tampering and Reverse Engineering
Attackers can reverse-engineer mobile apps to find vulnerabilities or tamper with code, potentially introducing malware or bypassing security controls.
API Security Issues
Insecure APIs can lead to unauthorized access or data leaks. Vulnerabilities like inadequate authentication or excessive permissions make APIs a key target for attacks.
Misuse of App Permissions
Apps often request unnecessary permissions, which can be exploited by attackers to access device data or functions, compromising user privacy and security.
Insecure Data Storage
Mobile apps often store sensitive data on the device. If data is stored without encryption or in insecure locations (like public directories), attackers can easily access it.
Weak Authentication
Unreliable authentication mechanisms, such as poor password policies or the absence of multi-factor authentication, can allow attackers to bypass login screens and gain unauthorized access.
Outdated Cryptography
Using weak cryptographic algorithms to secure data can make it easier for attackers to decrypt sensitive information, compromising user data.
Unprotected App Updates
If mobile apps fail to validate updates or downloads securely, attackers can push malicious updates to users, leading to device compromise.
Jailbreaking/Rooting Detection Bypass
Many mobile apps fail to properly detect if a device has been jailbroken (iOS) or rooted (Android), which increases the risk of privilege escalation or app tampering.
Network-based Attacks
Mobile apps that don’t secure network traffic via encryption can expose data to man-in-the-middle attacks, allowing attackers to intercept sensitive information.
Unsecured Data Transmission
Lack of encryption in network communications, exposing user data during transmission.
Our mobile application penetration testing services offer aholistic approach
Manual testing
At Iterasec, a leading pentesting company, our manual testing approach is designed to simulate real-world attackers, not just machines. Hence, effective pen testing is manual only to go beyond what scanners can find and simulate real adversaries.
Remediation
As part of our comprehensive web application security testing services, we provide support to fix the identified vulnerabilities properly. Free re-test included within three months after report delivery.
Solid report
Get a professional pentest report as part of our web app pentesting services with detailed finding descriptions and analysis of the work performed. On top of that, we provide an attestation letter you can show to your clients.
Not just pentesting
Pentesting is just the first step. We holistically help you build an efficient application security program and protect your infrastructure.
Why Choose Our Mobile Application Security Testing Company
We combine innovative pentest tactics and our experience to analyze your software for exploitable vulnerabilities and strengthen your security posture. Working with Iterasec, you get compliance with PCI, HIPAA, SOC2,3, OWASP, and more, an independent evaluation of your software and infrastructure security, and increased software quality thanks to avoiding critical security vulnerabilities. Iterasec ensures:Expert Cybersecurity Team
Our team of security experts finds juicier and more complex security vulnerabilities than other vendors.
Pragmatic Approach
We start with threat modeling and tailor our testing methodologies to suit your specific application requirements.
Delivery Quality
On-time, clear communication, proactive. Underpromise, overdeliver – that’s our motto.
Ready to protect your mobile applications from security threats? Contact us today to discover how our mobile app penetration testing services can enhance your app’s security.
Contact usExpert Cybersecurity Team
Cybersecurity is an industry of constant learning. Each of our colleagues has a professional and certification development plan.
Optimal approach to secure your business with professional Mobile Application Penetration Testing Services
Depending on the testing scope and input/data provided, mobile app pentesting services can be done in black, white or gray box mode.
Black box pentest
The client provides no or minimum input, such as IP address or company/domain name. While it simulates real-world scenarios, commercial pentests are still quite limited with the time-box.
Suitable for:
- attack simulation
- red teaming
Gray box pentest
The client provides information about the system, such as test credentials or even documentation. No source code is provided. In most of the cases, this is the most optimal type.
Suitable for:
- most of the pentests
White box pentest
Full information is provided, including source code, system documentation, etc. The big benefit is that due to code access, pentesters can reveal security issues from the inside.
Suitable for:
- product or application-level pentests
- codebase security review
Discover all steps how Iterasec mobile application penetration testing services work
During our audit, we rely on the NIST, OWASP, OSSTM, CIS Benchmark, and other methodologies. While employing some automated scanning tools, we also perform manual expert security testing: such an approach proves to be the most practically valuable.
We keep clients informed in the course of the project, providing regular status updates and immediate notifications for critical findings.
- 1A kick-off meeting to agree on the scope, inputs and communication
- 2Cloud pentest (2-5 weeks, depending on the scope)
- 3The final report that highlights the identified cloud security issues
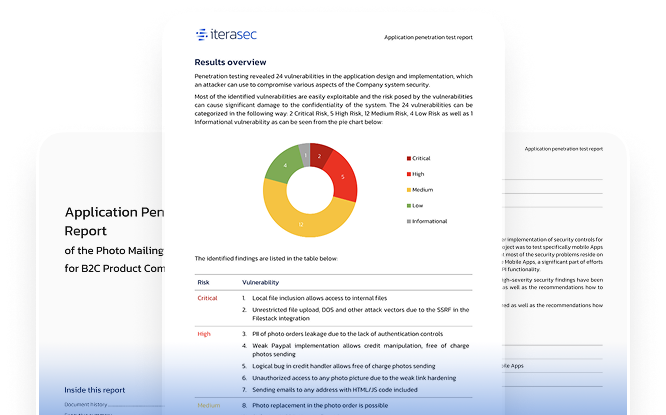
Explore our sample security testing service report
Request our sample security testing service report by contacting us today.
Contact usWhat our clients say
Awards and Recognitions
2023
Top cybersecurity consulting company
2023
Top cybersecurity consulting company
2023
Top ponetration testing company
Discover All Our Cybersecurity Services
FAQs
The cost of mobile application penetration testing services varies depending on the scope of the test and the complexity of the application. Contact us for a tailored quote based on your specific requirements.
Yes, mobile app penetration testing can be performed on live applications, though certain precautions may need to be taken to avoid disruptions. We work closely with you to ensure the test is carried out safely and effectively.
To prepare for mobile app pentesting, ensure that all necessary documentation and access credentials are ready. It’s also important to back up any critical data and notify key stakeholders about the test to minimize disruptions.
Failing to conduct mobile app penetration testing can leave your app vulnerable to attacks such as data breaches, unauthorized access, and malware injection. This can result in loss of sensitive user data, reputational damage, financial losses, and potential legal liabilities due to non-compliance with industry regulations.
Every industry benefits greatly from mobile app pentesting, however, industries such as finance, healthcare, e-commerce, and telecommunications have special needs in mobile app penetration testing services. These sectors handle sensitive data and must comply with stringent regulations (e.g., PCI DSS, HIPAA) to protect user information and ensure the security of their mobile applications.
Contacts
Please tell us what are you looking for and we will happily support you in that. Feel free to use our contact form or contact us directly.
Thank you for submission!
We’ve received your request and will get back to you shortly. If you have any urgent questions, feel free to contact us at [email protected]