Please tell us what are you looking for and we will happily support you in that.
Feel free to use our contact form or contact us directly.
Why Container Security Testing Services are Important
Container Security Testing Services are vital to ensure the unique security challenges posed by containerized applications are addressed effectively. Our testing targets critical aspects such as container orchestration, image vulnerabilities, and runtime configurations. Our experts analyze cluster setups, evaluate security hygiene, and explore known attacks to understand the impact of a microservice compromise, focusing on maintaining strong defenses against common and sophisticated security threats.
Microservices architectures are highly dynamic, allowing organizations to update and scale services independently, leading to an improved feature velocity. However, traditional security measures are not enough to protect these cloud-native architectures. Our container security testing services aim to address these complexities by ensuring that security evolves along with your development processes, and remains effective against emerging vulnerabilities.
As companies adopt multi-cloud strategies, it becomes challenging to maintain consistent security and compliance across diverse environments. Our container security audit services offer essential visibility and security evaluations across different cloud providers and configurations, ranging from Kubernetes to fully managed CaaS. We ensure that your containerized infrastructure meets strict security standards.
It is essential to keep up with known vulnerabilities and timely vendor patches as modern applications often rely on third-party and open-source components. Our container security audit thoroughly examines your software supply chain. We integrate security into your developer and DevOps tools to help manage compliance and reduce risks associated with these dependencies.
Our Container Security Audit Services deliver comprehensive insights and enhancements to your container environments. By thoroughly testing and evaluating each component, we provide actionable recommendations to strengthen your security. Here’s what you can expect from each area of our audit:
Our audits examine your cluster setup, including the correctness of configuration, testing access controls like Kubectl and RBAC, and evaluating network policies. We ensure your cluster's architecture is optimized for performance and maximum security, safeguarding your infrastructure against unauthorized access and potential breaches.
We evaluate your system's security hygiene, focusing on critical aspects such as timely updates, deployment of a minimal OS for reduced vulnerabilities, appropriate IAM roles, and effective monitoring and audit logging practices. Our team also verifies deployed binaries to confirm their integrity and compliance with security standards, ensuring your environment adheres to best practices in operational security.
Our container security services include a thorough assessment of your defenses against known attacks. It involves disabling default tokens and dashboards that could be potential security risks and scanning container images for known vulnerabilities. We help you fortify your containers against common exploitations by proactively addressing these issues.
Our audits assess how your security policies, secret protection measures, sandboxing practices, and mechanisms for authentication and encryption could be affected in the event of a compromise. We provide strategies to enhance these areas, ensuring each microservice is individually secure and contributes to your overall security.
Our security expertise extends to the leading containerization technologies, Kubernetes and OpenShift, addressing their unique security challenges. Both platforms are thoroughly tested to safeguard against vulnerabilities, ensuring your deployments are secure and resilient.
As the primary platform for orchestrating containerized workloads, Kubernetes automates deployment, scaling, and operations across clusters. Our testing services focus on identifying misconfigurations, ensuring robust access controls, and securing network policies and inter-container communications.
Developed by Red Hat, OpenShift enhances Kubernetes by adding advanced security features and monitoring capabilities, supporting continuous development and deployment. Our security checks ensure compliance and governance throughout the application lifecycle, from source to deployment.
Our team of security experts finds juicier and more complex security vulnerabilities than other vendors.
We start with threat modeling and tailor our testing methodologies to suit your specific application requirements.
On-time, clear communication, proactive. Underpromise, overdeliver – that’s our motto.
Cybersecurity is an industry of constant learning. Each of our colleagues has a professional and certification development plan.
During our audit, we rely on the NIST, OWASP, OSSTM, CIS Benchmark, and other methodologies. While employing some automated scanning tools, we also perform manual expert security testing: such an approach proves to be the most practically valuable.
We keep clients informed in the course of the project, providing regular status updates and immediate notifications for critical findings.
Discover all the steps in our container security services process:
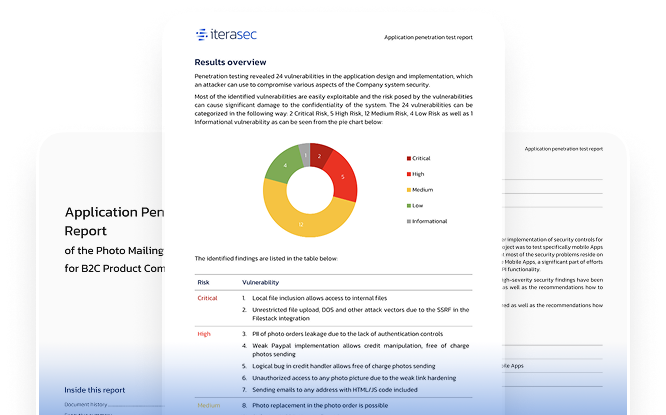
Please contact us, and we will send you a sample report covering several applications.
Contact usTop cybersecurity consulting company
Top cybersecurity consulting company
Top ponetration testing company
Container security testing is a comprehensive security evaluation method that identifies potential vulnerabilities in containerized environments by mimicking sophisticated cyberattacks. It focuses on various aspects such as container orchestration, image vulnerabilities, runtime configurations, and cluster setups. This testing is crucial for uncovering flaws that could compromise the integrity and confidentiality of containerized applications.
The main benefits of container security testing services include:
Enhanced Security Posture: Targets specific container vulnerabilities, improving defenses against attacks like container escape and image poisoning.
Compliance Assurance: Helps ensure that container deployments across different environments meet regulatory standards and industry compliance, maintaining trust and legal compliance.
Operational Resilience: Continuously assesses and addresses vulnerabilities, reducing downtime and enhancing system stability.
Integration with DevOps: Secures the CI/CD pipeline, aligning security practices with rapid development cycles.
Advanced Threat Detection: Uses sophisticated tools for in-depth threat analysis and management, including behavioral analytics and machine learning.
Container security audits should be conducted regularly, especially in environments that frequently update or change container deployments. Ideally, testing should be aligned with major updates or releases, and at least annually to ensure ongoing security and compliance. More frequent testing may be necessary for environments with high-risk profiles or those subject to strict regulatory requirements.
Container security audits can uncover a wide range of vulnerabilities specific to containerized environments, including:
Misconfigurations: Incorrect settings in container orchestration, network policies, or runtime configurations that could lead to unauthorized access.
Security Flaws in Container Images: Vulnerabilities within container images such as outdated libraries or insecure software components.
Orchestration Level Issues: Flaws in the management of container clusters that could allow attackers to manipulate or disrupt operations.
Runtime Vulnerabilities: Issues that occur when containers are running, including exploitation of shared resources or improper isolation that could lead to cross-container attacks.
Issues with DevOps and CI/CD Pipelines: Security weaknesses within the integration and deployment processes that could be exploited to introduce malicious code or disrupt service operations.
These vulnerabilities, if left unchecked, can lead to serious security breaches, making penetration testing an essential part of maintaining a secure containerized environment.
Please tell us what are you looking for and we will happily support you in that.
Feel free to use our contact form or contact us directly.