Why Cloud Security Testing Services are Important
Cloud security pentesting services are crucial for addressing the unique challenges posed by cloud environments. These services focus on critical aspects such as cloud infrastructure, application security, and data protection. Our experts analyze cloud setups, evaluate security hygiene, and explore known attacks to understand the impact of potential breaches, ensuring strong defenses against common and sophisticated threats.
Cloud Platforms We Cover

AWS (Amazon Web Services)
A comprehensive suite of on-demand cloud services, offering scalability, reliability, and global reach for businesses of all sizes.
Microsoft Azure
An enterprise-grade cloud platform seamlessly integrating with Microsoft tools and services to deliver secure, hybrid-ready solutions.
Google Cloud Platform
A robust, AI-driven infrastructure designed for high-performance computing, data analytics, and rapid innovation at scale.
On-Prem
Locally hosted environments where organizations maintain full control over hardware, software, and security within their own facilities.
Cloud Security Configuration Audit
When addressing the issue of misconfigurations, multiple factors must be considered. Our team conducts thorough security checks on your cloud system, targeting the most common security issues and misconfigurations:
User Management
Authentication, authorization, and access policies.
Component Isolation
Security groups, VPN settings, and Ingress/Egress routing.
Object Storage Visibility
Security of services like S3.
Serverless Function Security
Protection for serverless functions, such as Lambdas.
Metadata WebServices Hardening
Ensuring protection against SSRF vulnerabilities.
Data Encryption
Safeguarding data-in-transit and data-at-rest.
Key & Secret Management
Implementation of secure vaults.
Logging & Monitoring
Continuous visibility and oversight.
DFIR-Readiness
DFIR-Readiness
Cloud Penetration Testing
Our cloud penetration testing service focuses on evaluating two critical vectors:
Types of Vulnerabilities Our Cloud Penetration Testing Company Can Detect
Our cloud penetration testing services are designed to uncover a wide range of vulnerabilities in cloud environments. This comprehensive analysis ensures your cloud environment is protected against a wide range of potential threats. The vulnerabilities include:
Initial Access
Identifying weaknesses that could allow unauthorized entry into your cloud environment.
Execution
Detecting vulnerabilities that may permit the execution of malicious code or unauthorized commands.
Persistence
Uncovering methods attackers could use to maintain access to compromised systems.
Privilege Escalation
Identifying potential paths for attackers to gain elevated permissions within your cloud infrastructure.
Defense Evasion
Finding tactics used to avoid detection by security measures.
Credential Access
Detecting risks that could lead to the exposure or theft of credentials.
Discovery
Uncovering vulnerabilities that allow attackers to gather information about your cloud environment.
Lateral Movement
Identifying weaknesses that could enable attackers to move within your cloud environment.
Collection
Detecting vulnerabilities that could allow attackers to gather sensitive data.
Exfiltration
Identifying potential paths for data to be removed from your cloud environment.
Impact
Detecting vulnerabilities that could lead to data destruction or service disruption.
Why Choose Our Cloud Penetration Testing Services
Iterasec cloud security audits are distinguished by our:Expert Cybersecurity Team
Our team of security experts finds juicier and more complex security vulnerabilities than other vendors.
Pragmatic Approach
We start with threat modeling and tailor our testing methodologies to suit your specific application requirements.
Delivery Quality
On-time, clear communication, proactive. Underpromise, overdeliver – that’s our motto.
Ready to secure your cloud environment? Contact us to discover how our cloud penetration testing services can fortify your digital assets against emerging threats.
Contact usExpert Cybersecurity Team
Cybersecurity is an industry of constant learning. Each of our colleagues has a professional and certification development plan.
Discover All Steps How Iterasec cloud security testing services work
During our audit, we rely on the NIST, OWASP, OSSTM, CIS Benchmark, and other methodologies. While employing some automated scanning tools, we also perform manual expert security testing: such an approach proves to be the most practically valuable.
We keep clients informed in the course of the project, providing regular status updates and immediate notifications for critical findings.
Discover all the steps in our cloud security services process:
- 1A kick-off meeting to agree on the scope, inputs and communication
- 2Cloud pentest (2-5 weeks, depending on the scope)
- 3The final report that highlights the identified cloud security issues
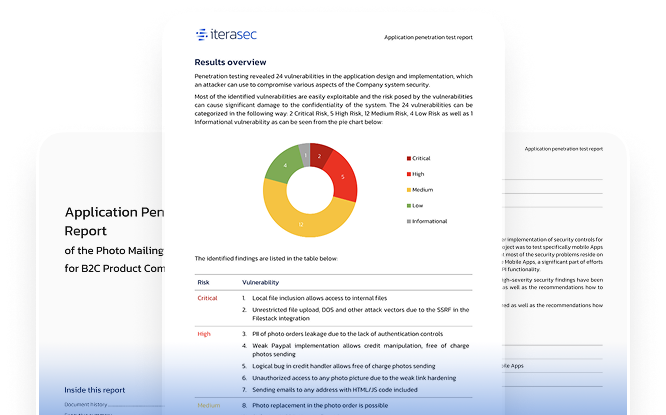
Explore our sample security testing service report
Request our sample security testing service report by contacting us today.
Contact usWhat our clients say
Awards and Recognitions
2023
Top cybersecurity consulting company
2023
Top cybersecurity consulting company
2023
Top ponetration testing company
Discover All Our Cybersecurity Services
FAQs
Cloud security testing services help by identifying and addressing vulnerabilities in your cloud environment, ensuring robust defenses against cyber threats, and maintaining compliance with industry standards.
Yes, cloud penetration testing services can help prevent data breaches by uncovering and mitigating security weaknesses before attackers can exploit them.
Cloud penetration testing should be conducted regularly, especially after major updates or changes in your cloud environment. Ideally, testing should be performed annually to ensure ongoing security and compliance.
The key deliverables of a cloud security audit include:
Detailed Security Report: A comprehensive document outlining identified vulnerabilities, their severity, and potential impacts.
Risk Assessment: Evaluate the risk level associated with each identified vulnerability.
Actionable Recommendations: Practical steps and strategies to mitigate identified risks and enhance security.
Compliance Check: An assessment of your cloud environment’s adherence to regulatory requirements and industry standards.
Security Overview: A summary of your current security posture, highlighting strengths and areas for improvement.
Incident Response Plan: Suggestions for improving or implementing an effective incident response plan tailored to your cloud infrastructure.
Iterasec can help secure your cloud infrastructure through a range of expert services and solutions:
Comprehensive Penetration Testing: Identifying and addressing vulnerabilities across your cloud environment through thorough testing and analysis.
Configuration and Compliance Audits: Ensuring your cloud setups comply with industry standards and best practices, minimizing the risk of misconfigurations.
Continuous Monitoring and Threat Detection: Implementing advanced monitoring tools to detect and respond to potential threats in real time.
Identity and Access Management (IAM) Optimization: Reviewing and optimizing IAM policies to prevent unauthorized access and enhance security controls.
Security Integration in DevOps: Embedding security practices within your CI/CD pipelines, ensuring that security is a continuous priority throughout the development lifecycle.
Tailored Security Solutions: Providing customized security strategies and solutions that align with your specific cloud infrastructure and business needs.
You can enhance your cloud security, mitigate risks, and ensure the integrity and confidentiality of your cloud-hosted data and applications using Iterasec expertise.
Contacts
Please tell us what are you looking for and we will happily support you in that. Feel free to use our contact form or contact us directly.
Thank you for submission!
We’ve received your request and will get back to you shortly. If you have any urgent questions, feel free to contact us at [email protected]